Using the ip classless command
7.2.3
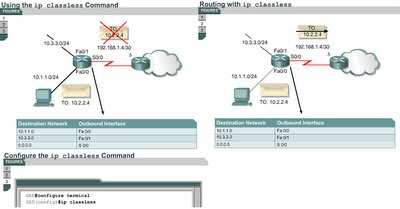
This page will explain what the ip classless command is and how it is used.Sometimes a router receives packets destined for an unknown subnet of a network that has directly connected subnets. Use the ip classless global configuration command to instruct the Cisco IOS software to forward these packets to the best supernet route. A supernet route is a route that covers a greater range of subnets with a single entry. For example, if an enterprise uses the entire subnet 10.10.0.0 /16, then a supernet route for 10.10.10.0 /24 would be 10.10.0.0 /16. The ip classless command is enabled by default in Cisco IOS Software Release 11.3 and later. To disable this feature, use the no form of this command.
When this feature is disabled any packets received that are destined for a subnet that falls within the subnetwork addressing scheme of the router will be discarded.
IP classless only affects the operation of the forwarding processes in IOS. IP classless does not affect the way the routing table is built. This is the essence of classful routing. If one part of a major network is known, but the subnet toward which the packet is destined within that major network is unknown, the packet is dropped.
The most confusing aspect of this rule is that the router only uses the default route if the major network destination does not exist in the routing table. A router by default assumes that all subnets of a directly connected network should be present in the routing table. If a packet is received with an unknown destination address within an unknown subnet of a directly attached network, the router assumes that the subnet does not exist. So the router will drop the packet even if there is a default route. To resolve this problem, configure ip classless on the router. This allows the router to ignore the classful boundaries of the networks in its routing table and simply route to the default route.
The Lab Activity will help students become more familiar with the ip classless command.
The next page describes some methods that are used to reduce routing loops.
Comments
Post a Comment