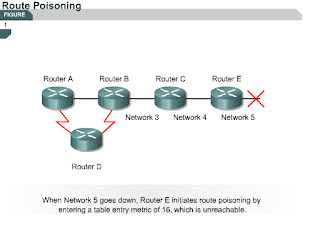
Route poisoning
7.1.5 This page will explain what route poisoning is and why it is used.
Route poisoning is used by various distance vector protocols to overcome large routing loops and offer detailed information when a subnet or network is not accessible. To accomplish this, the hop count is usually set to one more than the maximum.
One way to avoid inconsistent updates is route poisoning. When Network 5 goes down, Router E will set a distance of 16 for Network 5 to poison the route. This indicates that the network is unreachable.
When route poisoning is used with triggered updates it will speed up convergence time because neighboring routers do not have to wait 30 seconds before they advertise the poisoned route.
Route poisoning causes a routing protocol to advertise infinite-metric routes for a failed route. Route poisoning does not break split horizon rules. Split horizon with poison reverse is route poisoning that is placed on links that split horizon would not normally allow routing information to flow across. In either case, the result is that failed routes are advertised with infinite metrics.
The next page will discuss how triggered updates can prevent routing loops.
Comments
Post a Comment