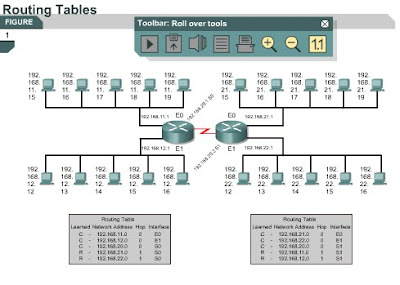
Routing tables
10.2.5 This page will describe the functions of a routing table.
Routers use routing protocols to build and maintain routing tables that contain route information. This aids in the process of path determination. Routing protocols fill routing tables with a variety of route information. This information varies based on the routing protocol used. Routing tables contain the information necessary to forward data packets across connected networks. Layer 3 devices interconnect broadcast domains or LANs. A hierarchical address scheme is required for data transfers.
Routers keep track of the following information in their routing tables:
• Protocol type – Identifies the type of routing protocol that created each entry.
• Next-hop associations – Tell a router that a destination is either directly connected to the router or that it can be reached through another router called the next-hop on the way to the destination. When a router receives a packet, it checks the destination address and attempts to match this address with a routing table entry.
• Routing metric – Different routing protocols use different routing metrics. Routing metrics are used to determine the desirability of a route. For example, RIP uses hop count as its only routing metric. IGRP uses bandwidth, load, delay, and reliability metrics to create a composite metric value.
• Outbound interfaces – The interface that the data must be sent out of to reach the final destination.
Routers communicate with one another to maintain their routing tables through the transmission of routing update messages. Some routing protocols transmit update messages periodically. Other protocols send them only when there are changes in the network topology. Some protocols transmit the entire routing table in each update message and some transmit only routes that have changed. Routers analyze the routing updates from directly-connected routers to build and maintain their routing tables.
The next page will explain routing algorithms and metrics.
Routing algorithms and metrics
10.2.6 This page will define algorithms and metrics as they relate to routers.
An algorithm is a detailed solution to a problem. Different routing protocols use different algorithms to choose the port to which a packet should be sent. Routing algorithms depend on metrics to make these decisions.
Routing protocols often have one or more of the following design goals:
• Optimization – This is the capability of a routing algorithm to select the best route. The route will depend on the metrics and metric weights used in the calculation. For example, one algorithm may use both hop count and delay metrics, but may consider delay metrics as more important in the calculation.
• Simplicity and low overhead – The simpler the algorithm, the more efficiently it will be processed by the CPU and memory in the router. This is important so that the network can scale to large proportions, such as the Internet.
• Robustness and stability – A routing algorithm should perform correctly when confronted by unusual or unforeseen circumstances, such as hardware failures, high load conditions, and implementation errors.
• Flexibility – A routing algorithm should quickly adapt to a variety of network changes. These changes include router availability, router memory, changes in bandwidth, and network delay.
• Rapid convergence – Convergence is the process of agreement by all routers on available routes. When a network event causes changes in router availability, updates are needed to reestablish network connectivity. Routing algorithms that converge slowly can cause data to be undeliverable.
Routing algorithms use different metrics to determine the best route. Each routing algorithm interprets what is best in its own way. A routing algorithm generates a number called a metric value for each path through a network. Sophisticated routing algorithms base route selection on multiple metrics that are combined in a composite metric value.
Typically, smaller metric values indicate preferred paths.
Metrics can be based on a single characteristic of a path, or can be calculated based on several characteristics. The following metrics are most commonly used by routing protocols:
• Bandwidth – Bandwidth is the data capacity of a link. Normally, a 10-Mbps Ethernet link is preferable to a 64-kbps leased line.
• Delay – Delay is the length of time required to move a packet along each link from a source to a destination. Delay depends on the bandwidth of intermediate links, the amount of data that can be temporarily stored at each router, network congestion, and physical distance.
• Load – Load is the amount of activity on a network resource such as a router or a link.
• Reliability – Reliability is usually a reference to the error rate of each network link.
• Hop count – Hop count is the number of routers that a packet must travel through before reaching its destination. Each router is equal to one hop. A hop count of four indicates that data would have to pass through four routers to reach its destination. If multiple paths are available to a destination, the path with the least number of hops is preferred.
• Ticks – The delay on a data link using IBM PC clock ticks. One tick is approximately 1/18 second.
• Cost – Cost is an arbitrary value, usually based on bandwidth, monetary expense, or other measurement, that is assigned by a network administrator.
The next page will discuss two types of routing protocols.
Tuesday, March 23, 2010
Thursday, March 18, 2010
Routed versus routing / Path determination
Routed versus routing
10.2.3 This page explains the differences between routing protocols and routed protocols.
Routed or routable protocols are used at the network layer to transfer data from one host to another across a router. Routed protocols transport data across a network. Routing protocols allow routers to choose the best path for data from a source to a destination.
Some functions of a routed protocol are as follows:
• Includes any network protocol suite that provides enough information in its network layer address to allow a router to forward it to the next device and ultimately to its destination
• Defines the format and use of the fields within a packet
The Internet Protocol (IP) and Novell Internetwork Packet Exchange (IPX) are examples of routed protocols. Other examples include DECnet, AppleTalk, Banyan VINES, and Xerox Network Systems (XNS).
Routers use routing protocols to exchange routing tables and share routing information. In other words, routing protocols enable routers to route routed protocols.
Some functions of a routing protocol are as follows:
• Provides processes used to share route information
• Allows routers to communicate with other routers to update and maintain the routing tables
Examples of routing protocols that support the IP routed protocol include RIP, IGRP, OSPF, BGP, and EIGRP.
Path determination
10.2.4 This page will explain how path determination occurs.
Path determination occurs at the network layer. A router uses path determination to compare a destination address to the available routes in its routing table and select the best path. The routers learn of these available routes through static routing or dynamic routing. Routes configured manually by the network administrator are static routes. Routes learned by others routers using a routing protocol are dynamic routes.
The router uses path determination to decide which port to send a packet out of to reach its destination. This process is also referred to as routing the packet. Each router that the packet encounters along the way is called a hop. The hop count is the distanced traveled. Path determination can be compared to a person who drives from one location in a city to another. The driver has a map that shows which streets lead to the destination, just as a router has a routing table. The driver travels from one intersection to another just as a packet travels from one router to another in each hop. At any intersection, the driver can choose to turn left, turn right, or go straight ahead. This is similar to how a router chooses the outbound port through which a packet is sent.
The decisions of a driver are influenced by factors such as traffic, the speed limit, the number of lanes, tolls, and whether or not a road is frequently closed. Sometimes it is faster to take a longer route on a smaller, less crowded back street instead of a highway with a lot of traffic. Similarly, routers can make decisions based on the load, bandwidth, delay, cost, and reliability of a network link.
The following process is used to determine the path for every packet that is routed:
• The router compares the IP address of the packet that it received to the IP tables that it has.
• The destination address is obtained from the packet.
• The mask of the first entry in the routing table is applied to the destination address.
• The masked destination and the routing table entry are compared.
• If there is a match, the packet is forwarded to the port that is associated with that table entry.
• If there is not a match, the next entry in the table is checked.
• If the packet does not match any entries in the table, the router checks to see if a default route has been set.
• If a default route has been set, the packet is forwarded to the associated port. A default route is a route that is configured by the network administrator as the route to use if there are no matches in the routing table.
• If there is no default route, the packet is discarded. A message is often sent back to the device that sent the data to indicate that the destination was unreachable.
The next page will explain how routing protocols build and maintain routing tables.
10.2.3 This page explains the differences between routing protocols and routed protocols.
Routed or routable protocols are used at the network layer to transfer data from one host to another across a router. Routed protocols transport data across a network. Routing protocols allow routers to choose the best path for data from a source to a destination.
Some functions of a routed protocol are as follows:
• Includes any network protocol suite that provides enough information in its network layer address to allow a router to forward it to the next device and ultimately to its destination
• Defines the format and use of the fields within a packet
The Internet Protocol (IP) and Novell Internetwork Packet Exchange (IPX) are examples of routed protocols. Other examples include DECnet, AppleTalk, Banyan VINES, and Xerox Network Systems (XNS).
Routers use routing protocols to exchange routing tables and share routing information. In other words, routing protocols enable routers to route routed protocols.
Some functions of a routing protocol are as follows:
• Provides processes used to share route information
• Allows routers to communicate with other routers to update and maintain the routing tables
Examples of routing protocols that support the IP routed protocol include RIP, IGRP, OSPF, BGP, and EIGRP.
Path determination
10.2.4 This page will explain how path determination occurs.
Path determination occurs at the network layer. A router uses path determination to compare a destination address to the available routes in its routing table and select the best path. The routers learn of these available routes through static routing or dynamic routing. Routes configured manually by the network administrator are static routes. Routes learned by others routers using a routing protocol are dynamic routes.
The router uses path determination to decide which port to send a packet out of to reach its destination. This process is also referred to as routing the packet. Each router that the packet encounters along the way is called a hop. The hop count is the distanced traveled. Path determination can be compared to a person who drives from one location in a city to another. The driver has a map that shows which streets lead to the destination, just as a router has a routing table. The driver travels from one intersection to another just as a packet travels from one router to another in each hop. At any intersection, the driver can choose to turn left, turn right, or go straight ahead. This is similar to how a router chooses the outbound port through which a packet is sent.
The decisions of a driver are influenced by factors such as traffic, the speed limit, the number of lanes, tolls, and whether or not a road is frequently closed. Sometimes it is faster to take a longer route on a smaller, less crowded back street instead of a highway with a lot of traffic. Similarly, routers can make decisions based on the load, bandwidth, delay, cost, and reliability of a network link.
The following process is used to determine the path for every packet that is routed:
• The router compares the IP address of the packet that it received to the IP tables that it has.
• The destination address is obtained from the packet.
• The mask of the first entry in the routing table is applied to the destination address.
• The masked destination and the routing table entry are compared.
• If there is a match, the packet is forwarded to the port that is associated with that table entry.
• If there is not a match, the next entry in the table is checked.
• If the packet does not match any entries in the table, the router checks to see if a default route has been set.
• If a default route has been set, the packet is forwarded to the associated port. A default route is a route that is configured by the network administrator as the route to use if there are no matches in the routing table.
• If there is no default route, the packet is discarded. A message is often sent back to the device that sent the data to indicate that the destination was unreachable.
The next page will explain how routing protocols build and maintain routing tables.
Routing versus switching
Routing versus switching
10.2.2 This page will compare and contrast routing and switching. Routers and switches may seem to perform the same function. The primary difference is that switches operate at Layer 2 of the OSI model and routers operate at Layer 3. This distinction indicates that routers and switches use different information to send data from a source to a destination.
The relationship between switching and routing can be compared to local and long-distance telephone calls. When a telephone call is made to a number within the same area code, a local switch handles the call. The local switch can only keep track of its local numbers. The local switch cannot handle all the telephone numbers in the world. When the switch receives a request for a call outside of its area code, it switches the call to a higher-level switch that recognizes area codes. The higher-level switch then switches the call so that it eventually gets to the local switch for the area code dialed.
The router performs a function similar to that of the higher-level switch in the telephone example. Figure shows the ARP tables for Layer 2 MAC addresses and routing tables for Layer 3 IP addresses. Each computer and router interface maintains an ARP table for Layer 2 communication. The ARP table is only effective for the broadcast domain to which it is connected. The router also maintains a routing table that allows it to route data outside of the broadcast domain. Each ARP table entry contains an IP-MAC address pair.
The Layer 2 switch builds its forwarding table using MAC addresses. When a host has data for a non-local IP address, it sends the frame to the closest router. This router is also known as its default gateway. The host uses the MAC address of the router as the destination MAC address.
A switch interconnects segments that belong to the same logical network or subnetwork. For non-local hosts, the switch forwards the frame to the router based on the destination MAC address. The router examines the Layer 3 destination address of the packet to make the forwarding decision. Host X knows the IP address of the router because the IP configuration of the host contains the IP address of the default gateway.
Just as a switch keeps a table of known MAC addresses, the router keeps a table of IP addresses known as a routing table. MAC addresses are not logically organized. IP addresses are organized in a hierarchy. A switch can handle a limited number of unorganized MAC addresses since it only has to search its table for addresses within its segment. Routers require an organized address system that can group similar addresses together and treat them as a single network unit until the data reaches the destination segment.
If IP addresses were not organized, the Internet would not work. This could be compared to a library that contained millions of individual pages of printed material in a large pile. This material is useless because it is impossible to locate an individual document. If the pages are identified and organized into books and each book is listed in a book index, it will be a lot easier to locate and use the data.
Another difference between switched and routed networks is switched networks do not block broadcasts. As a result, switches can be overwhelmed by broadcast storms. Routers block LAN broadcasts, so a broadcast storm only affects the broadcast domain from which it originated. Since routers block broadcasts, they also provide a higher level of security and bandwidth control than switches.
The next page will compare routing and routed protocols.
10.2.2 This page will compare and contrast routing and switching. Routers and switches may seem to perform the same function. The primary difference is that switches operate at Layer 2 of the OSI model and routers operate at Layer 3. This distinction indicates that routers and switches use different information to send data from a source to a destination.
The relationship between switching and routing can be compared to local and long-distance telephone calls. When a telephone call is made to a number within the same area code, a local switch handles the call. The local switch can only keep track of its local numbers. The local switch cannot handle all the telephone numbers in the world. When the switch receives a request for a call outside of its area code, it switches the call to a higher-level switch that recognizes area codes. The higher-level switch then switches the call so that it eventually gets to the local switch for the area code dialed.
The router performs a function similar to that of the higher-level switch in the telephone example. Figure shows the ARP tables for Layer 2 MAC addresses and routing tables for Layer 3 IP addresses. Each computer and router interface maintains an ARP table for Layer 2 communication. The ARP table is only effective for the broadcast domain to which it is connected. The router also maintains a routing table that allows it to route data outside of the broadcast domain. Each ARP table entry contains an IP-MAC address pair.
The Layer 2 switch builds its forwarding table using MAC addresses. When a host has data for a non-local IP address, it sends the frame to the closest router. This router is also known as its default gateway. The host uses the MAC address of the router as the destination MAC address.
A switch interconnects segments that belong to the same logical network or subnetwork. For non-local hosts, the switch forwards the frame to the router based on the destination MAC address. The router examines the Layer 3 destination address of the packet to make the forwarding decision. Host X knows the IP address of the router because the IP configuration of the host contains the IP address of the default gateway.
Just as a switch keeps a table of known MAC addresses, the router keeps a table of IP addresses known as a routing table. MAC addresses are not logically organized. IP addresses are organized in a hierarchy. A switch can handle a limited number of unorganized MAC addresses since it only has to search its table for addresses within its segment. Routers require an organized address system that can group similar addresses together and treat them as a single network unit until the data reaches the destination segment.
If IP addresses were not organized, the Internet would not work. This could be compared to a library that contained millions of individual pages of printed material in a large pile. This material is useless because it is impossible to locate an individual document. If the pages are identified and organized into books and each book is listed in a book index, it will be a lot easier to locate and use the data.
Another difference between switched and routed networks is switched networks do not block broadcasts. As a result, switches can be overwhelmed by broadcast storms. Routers block LAN broadcasts, so a broadcast storm only affects the broadcast domain from which it originated. Since routers block broadcasts, they also provide a higher level of security and bandwidth control than switches.
The next page will compare routing and routed protocols.
Routing overview
Routing overview
10.2.1 This page will discuss routing and the two main functions of a router.
Routing is an OSI Layer 3 function. Routing is a hierarchical organizational scheme that allows individual addresses to be grouped together. These individual addresses are treated as a single unit until the destination address is needed for final delivery of the data. Routing finds the most efficient path from one device to another. The primary device that performs the routing process is the router.
The following are the two key functions of a router:
• Routers must maintain routing tables and make sure other routers know of changes in the network topology. They use routing protocols to communicate network information with other routers.
• When packets arrive at an interface, the router must use the routing table to determine where to send them. The router switches the packets to the appropriate interface, adds the frame information for the interface, and then transmits the frame.
A router is a network layer device that uses one or more routing metrics to determine the optimal path along which network traffic should be forwarded. Routing metrics are values that are used to determine the advantage of one route over another. Routing protocols use various combinations of metrics to determine the best path for data.
Routers interconnect network segments or entire networks. Routers pass data frames between networks based on Layer 3 information. Routers make logical decisions about the best path for the delivery of data. Routers then direct packets to the appropriate output port to be encapsulated for transmission. Stages of the encapsulation and de-encapsulation process occur each time a packet transfers through a router. The router must de-encapsulate the Layer 2 data frame to access and examine the Layer 3 address. As shown in Figure , the complete process of sending data from one device to another involves encapsulation and de-encapsulation on all seven OSI layers. The encapsulation process breaks up the data stream into segments, adds the appropriate headers and trailers, and then transmits the data. The de-encapsulation process removes the headers and trailers and then recombines the data into a seamless stream.
This course focuses on the most common routable protocol, which is IP. Other examples of routable protocols include IPX/SPX and AppleTalk. These protocols provide Layer 3 support. Non-routable protocols do not provide Layer 3 support. The most common non-routable protocol is NetBEUI. NetBEUI is a small, fast, and efficient protocol that is limited to frame delivery within one segment.
The next page will compare routing and switching.
10.2.1 This page will discuss routing and the two main functions of a router.
Routing is an OSI Layer 3 function. Routing is a hierarchical organizational scheme that allows individual addresses to be grouped together. These individual addresses are treated as a single unit until the destination address is needed for final delivery of the data. Routing finds the most efficient path from one device to another. The primary device that performs the routing process is the router.
The following are the two key functions of a router:
• Routers must maintain routing tables and make sure other routers know of changes in the network topology. They use routing protocols to communicate network information with other routers.
• When packets arrive at an interface, the router must use the routing table to determine where to send them. The router switches the packets to the appropriate interface, adds the frame information for the interface, and then transmits the frame.
A router is a network layer device that uses one or more routing metrics to determine the optimal path along which network traffic should be forwarded. Routing metrics are values that are used to determine the advantage of one route over another. Routing protocols use various combinations of metrics to determine the best path for data.
Routers interconnect network segments or entire networks. Routers pass data frames between networks based on Layer 3 information. Routers make logical decisions about the best path for the delivery of data. Routers then direct packets to the appropriate output port to be encapsulated for transmission. Stages of the encapsulation and de-encapsulation process occur each time a packet transfers through a router. The router must de-encapsulate the Layer 2 data frame to access and examine the Layer 3 address. As shown in Figure , the complete process of sending data from one device to another involves encapsulation and de-encapsulation on all seven OSI layers. The encapsulation process breaks up the data stream into segments, adds the appropriate headers and trailers, and then transmits the data. The de-encapsulation process removes the headers and trailers and then recombines the data into a seamless stream.
This course focuses on the most common routable protocol, which is IP. Other examples of routable protocols include IPX/SPX and AppleTalk. These protocols provide Layer 3 support. Non-routable protocols do not provide Layer 3 support. The most common non-routable protocol is NetBEUI. NetBEUI is a small, fast, and efficient protocol that is limited to frame delivery within one segment.
The next page will compare routing and switching.
Anatomy of an IP packet
Anatomy of an IP packet
10.1.5 IP packets consist of the data from upper layers plus an IP header. This page will discuss the information contained in the IP header:
• Version – Specifies the format of the IP packet header. The 4-bit version field contains the number 4 if it is an IPv4 packet and 6 if it is an IPv6 packet. However, this field is not used to distinguish between IPv4 and IPv6 packets. The protocol type field present in the Layer 2 envelope is used for that.
• IP header length (HLEN) – Indicates the datagram header length in 32-bit words. This is the total length of all header information and includes the two variable-length header fields.
• Type of service (ToS) – 8 bits that specify the level of importance that has been assigned by a particular upper-layer protocol.
• Total length – 16 bits that specify the length of the entire packet in bytes. This includes the data and header. To get the length of the data payload subtract the HLEN from the total length.
• Identification – 16 bits that identify the current datagram. This is the sequence number.
• Flags – A 3-bit field in which the two low-order bits control fragmentation. One bit specifies if the packet can be fragmented and the other indicates if the packet is the last fragment in a series of fragmented packets.
• Fragment offset – 13 bits that are used to help piece together datagram fragments. This field allows the previous field to end on a 16-bit boundary.
• Time to Live (TTL) – A field that specifies the number of hops a packet may travel. This number is decreased by one as the packet travels through a router. When the counter reaches zero the packet is discarded. This prevents packets from looping endlessly.
• Protocol – 8 bits that indicate which upper-layer protocol such as TCP or UDP receives incoming packets after the IP processes have been completed.
• Header checksum – 16 bits that help ensure IP header integrity.
• Source address – 32 bits that specify the IP address of the node from which the packet was sent.
• Destination address – 32 bits that specify the IP address of the node to which the data is sent.
• Options – Allows IP to support various options such as security. The length of this field varies.
• Padding – Extra zeros are added to this field to ensure that the IP header is always a multiple of 32 bits.
• Data – Contains upper-layer information and has a variable length of up to 64 bits.
While the IP source and destination addresses are important, the other header fields have made IP very flexible. The header fields list the source and destination address information of the packet and often indicate the length of the message data. The information for routing the message is also contained in IP headers, which can get long and complex
This page concludes this lesson. The next lesson will focus on IP routing protocols. The first page provides a routing overview.
10.1.5 IP packets consist of the data from upper layers plus an IP header. This page will discuss the information contained in the IP header:
• Version – Specifies the format of the IP packet header. The 4-bit version field contains the number 4 if it is an IPv4 packet and 6 if it is an IPv6 packet. However, this field is not used to distinguish between IPv4 and IPv6 packets. The protocol type field present in the Layer 2 envelope is used for that.
• IP header length (HLEN) – Indicates the datagram header length in 32-bit words. This is the total length of all header information and includes the two variable-length header fields.
• Type of service (ToS) – 8 bits that specify the level of importance that has been assigned by a particular upper-layer protocol.
• Total length – 16 bits that specify the length of the entire packet in bytes. This includes the data and header. To get the length of the data payload subtract the HLEN from the total length.
• Identification – 16 bits that identify the current datagram. This is the sequence number.
• Flags – A 3-bit field in which the two low-order bits control fragmentation. One bit specifies if the packet can be fragmented and the other indicates if the packet is the last fragment in a series of fragmented packets.
• Fragment offset – 13 bits that are used to help piece together datagram fragments. This field allows the previous field to end on a 16-bit boundary.
• Time to Live (TTL) – A field that specifies the number of hops a packet may travel. This number is decreased by one as the packet travels through a router. When the counter reaches zero the packet is discarded. This prevents packets from looping endlessly.
• Protocol – 8 bits that indicate which upper-layer protocol such as TCP or UDP receives incoming packets after the IP processes have been completed.
• Header checksum – 16 bits that help ensure IP header integrity.
• Source address – 32 bits that specify the IP address of the node from which the packet was sent.
• Destination address – 32 bits that specify the IP address of the node to which the data is sent.
• Options – Allows IP to support various options such as security. The length of this field varies.
• Padding – Extra zeros are added to this field to ensure that the IP header is always a multiple of 32 bits.
• Data – Contains upper-layer information and has a variable length of up to 64 bits.
While the IP source and destination addresses are important, the other header fields have made IP very flexible. The header fields list the source and destination address information of the packet and often indicate the length of the message data. The information for routing the message is also contained in IP headers, which can get long and complex
This page concludes this lesson. The next lesson will focus on IP routing protocols. The first page provides a routing overview.
Connectionless and connection-oriented delivery
Connectionless and connection-oriented delivery
10.1.4 This page will introduce two types of delivery systems, which are connectionless and connection-oriented.
These two services provide the actual end-to-end delivery of data in an internetwork.
Most network services use a connectionless delivery system. Different packets may take different paths to get through the network. The packets are reassembled after they arrive at the destination. In a connectionless system, the destination is not contacted before a packet is sent. A good comparison for a connectionless system is a postal system. The recipient is not contacted to see if they will accept the letter before it is sent. Also, the sender does not know if the letter arrived at the destination.
In connection-oriented systems, a connection is established between the sender and the recipient before any data is transferred. An example of a connection-oriented network is the telephone system. The caller places the call, a connection is established, and then communication occurs.
Connectionless network processes are often referred to as packet-switched processes. As the packets pass from source to destination, packets can switch to different paths, and possibly arrive out of order. Devices make the path determination for each packet based on a variety of criteria. Some of the criteria, such as available bandwidth, may differ from packet to packet.
Connection-oriented network processes are often referred to as circuit-switched processes. A connection with the recipient is first established, and then data transfer begins. All packets travel sequentially across the same physical or virtual circuit.
The Internet is a gigantic, connectionless network in which the majority of packet deliveries are handled by IP. TCP adds Layer 4, connection-oriented reliability services to IP.
The next page will discuss the IP header.
10.1.4 This page will introduce two types of delivery systems, which are connectionless and connection-oriented.
These two services provide the actual end-to-end delivery of data in an internetwork.
Most network services use a connectionless delivery system. Different packets may take different paths to get through the network. The packets are reassembled after they arrive at the destination. In a connectionless system, the destination is not contacted before a packet is sent. A good comparison for a connectionless system is a postal system. The recipient is not contacted to see if they will accept the letter before it is sent. Also, the sender does not know if the letter arrived at the destination.
In connection-oriented systems, a connection is established between the sender and the recipient before any data is transferred. An example of a connection-oriented network is the telephone system. The caller places the call, a connection is established, and then communication occurs.
Connectionless network processes are often referred to as packet-switched processes. As the packets pass from source to destination, packets can switch to different paths, and possibly arrive out of order. Devices make the path determination for each packet based on a variety of criteria. Some of the criteria, such as available bandwidth, may differ from packet to packet.
Connection-oriented network processes are often referred to as circuit-switched processes. A connection with the recipient is first established, and then data transfer begins. All packets travel sequentially across the same physical or virtual circuit.
The Internet is a gigantic, connectionless network in which the majority of packet deliveries are handled by IP. TCP adds Layer 4, connection-oriented reliability services to IP.
The next page will discuss the IP header.
Packet propagation and switching within a router
Packet propagation and switching within a router
10.1.3 This page will explain the process that occurs as a packet moves through a network.
As a packet travels through an internetwork to its final destination, the Layer 2 frame headers and trailers are removed and replaced at every Layer 3 device. This is because Layer 2 data units, or frames, are for local addressing. Layer 3 data units, or packets, are for end-to-end addressing.
Layer 2 Ethernet frames are designed to operate within a broadcast domain with the MAC address that is burned into the physical device. Other Layer 2 frame types include PPP serial links and Frame Relay connections, which use different Layer 2 addressing schemes. Regardless of the type of Layer 2 addressing used, frames are designed to operate within a Layer 2 broadcast domain. When the data is sent to a Layer 3 device the Layer 2 information changes.
As a frame is received at a router interface, the destination MAC address is extracted. The address is checked to see if the frame is directly addressed to the router interface, or if it is a broadcast. In either situation, the frame is accepted. Otherwise, the frame is discarded since it is destined for another device on the collision domain.
The CRC information is extracted from the frame trailer of an accepted frame. The CRC is calculated to verify that the frame data is without error.
If the check fails, the frame is discarded. If the check is valid, the frame header and trailer are removed and the packet is passed up to Layer 3. The packet is then checked to see if it is actually destined for the router, or if it is to be routed to another device in the internetwork. If the destination IP address matches one of the router ports, the Layer 3 header is removed and the data is passed up to the Layer 4. If the packet is to be routed, the destination IP address will be compared to the routing table. If a match is found or there is a default route, the packet will be sent to the interface specified in the matched routing table statement. When the packet is switched to the outgoing interface, a new CRC value is added as a frame trailer, and the proper frame header is added to the packet. The frame is then transmitted to the next broadcast domain on its trip to the final destination.
The next page will describe two types of delivery services.
10.1.3 This page will explain the process that occurs as a packet moves through a network.
As a packet travels through an internetwork to its final destination, the Layer 2 frame headers and trailers are removed and replaced at every Layer 3 device. This is because Layer 2 data units, or frames, are for local addressing. Layer 3 data units, or packets, are for end-to-end addressing.
Layer 2 Ethernet frames are designed to operate within a broadcast domain with the MAC address that is burned into the physical device. Other Layer 2 frame types include PPP serial links and Frame Relay connections, which use different Layer 2 addressing schemes. Regardless of the type of Layer 2 addressing used, frames are designed to operate within a Layer 2 broadcast domain. When the data is sent to a Layer 3 device the Layer 2 information changes.
As a frame is received at a router interface, the destination MAC address is extracted. The address is checked to see if the frame is directly addressed to the router interface, or if it is a broadcast. In either situation, the frame is accepted. Otherwise, the frame is discarded since it is destined for another device on the collision domain.
The CRC information is extracted from the frame trailer of an accepted frame. The CRC is calculated to verify that the frame data is without error.
If the check fails, the frame is discarded. If the check is valid, the frame header and trailer are removed and the packet is passed up to Layer 3. The packet is then checked to see if it is actually destined for the router, or if it is to be routed to another device in the internetwork. If the destination IP address matches one of the router ports, the Layer 3 header is removed and the data is passed up to the Layer 4. If the packet is to be routed, the destination IP address will be compared to the routing table. If a match is found or there is a default route, the packet will be sent to the interface specified in the matched routing table statement. When the packet is switched to the outgoing interface, a new CRC value is added as a frame trailer, and the proper frame header is added to the packet. The frame is then transmitted to the next broadcast domain on its trip to the final destination.
The next page will describe two types of delivery services.
Subscribe to:
Posts (Atom)